The Cybersecurity Generalist
Within many small and medium organizations (SMOs), and even within larger organizations that are not heavily reliant on internet-based activities, there are individuals tasked with cybersecurity responsibilities who may not have any IT or cybersecurity background. While not specifically the province of the NOS, this annex provides a more detailed description of cybersecurity competencies that can serve as a reference to employers, educators and workforce development professionals seeking a better understanding of the requirements of this role.
Applicable job titles: Corporate Security Officer, Security Analyst, Security Officer, Security Manager, etc.
Cybersecurity Generalists:
- Perform cybersecurity functions on a part-time basis in conjunction with other responsibilities;
- Only require cybersecurity knowledge, skills and abilities commensurate with their business, technical and threat context; and
- Are not considered cybersecurity professionals and do not have a cybersecurity career trajectory.
Common tasks include:
- Assess the organization’s cybersecurity posture
- Facilitate identification of organizational cyber risks
- Identify non-technical cybersecurity controls
- Identify and liaise with technical experts, internal or external, on technical controls
- Develop organizational cybersecurity plans and policies
- Advise leadership on security awareness and training
- Monitor and support technical experts, whether in-house or outsourced, in their cybersecurity functions
- Coordinate cybersecurity incident response
- Monitor and report on response and mitigation actions and recommend courses of action based on technical advice
- Coordinate post-mortem activities on events and incidents, integrating lessons learned into organizational policies and procedures
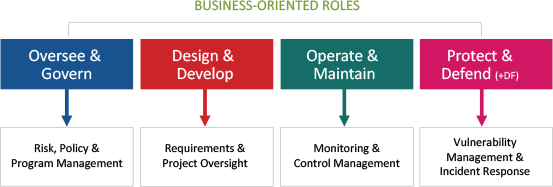
For many of these tasks, there are ample online resources available to guide the security generalists in their duties. Underpinning effectiveness in these tasks, however, are basic knowledge, skills and abilities (KSAs) needed to support decision making and action. However, it is unlikely that they will have any extensive cybersecurity training or education. Accordingly, they should be offered sufficient learning opportunities to attain the required competencies commensurate with their responsibilities as well as the threat, technical and business context. As shown in the examples in the figure below, this typically requires competencies borrowed from some of the work roles within each major work category.
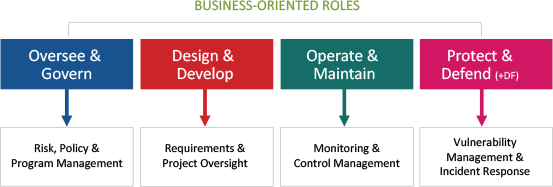
Figure – Cybersecurity generalist functions drawn from existing activity areas
Basic Knowledge:
- Technical context (e.g. organizational IT infrastructure, software, devices and policies)
- Cyber threat context (including deliberate, accidental, natural hazards)
- Business context (priorities, objectives, market, trends)
- Legal, policy and ethical context for security
- Cybersecurity risk management as part of organizational risk
- Cybersecurity incident management (domain specific)
- Cybersecurity processes, technology, trends and emerging issues
- Sources of cybersecurity expertise and resources
Basic Skills and Abilities:
- Providing business advice within the legal & policy cybersecurity context
- Exercising foresight and security planning to support digital business activities and growth
- Translating cyber risk to corporate risk
- Differentiating between compliance and risk
- Interpreting threat and risk assessments for the business context
- Assessing effectiveness of security controls against organizational security objectives
Common Competencies
For all the core cybersecurity roles regardless of activity area/work category, there are several common competencies that are applied at the basic, intermediate, or advanced level depending on the role. All cybersecurity professionals, regardless of role, should have a basic ability to apply the following in their work domain/context:
- IT systems and networking
- Systems architecture and models
- Internet protocols, systems, and devices
- Cybersecurity foundations
- Integrated security framework
- Cybersecurity strategies and approaches
- Threat landscape and common threat surfaces (personnel, physical, IT/logical, supply chain)